More and more websites ask visitors to approve notifications and browser changes and sometimes display messages on the user’s mobile phone or desktop computer. In many cases, these reports are benign, but some shady companies pay website owners to install their report scripts and then sell this communication channel to crooks and hackers.
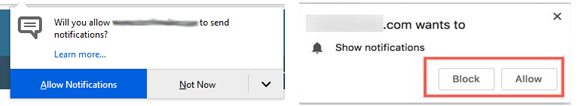
Notification tips in Firefox (links) and Google Chrome.
When a website you visit asks permission to send notifications and you approve the request, pop-up messages appear outside your browser. On Microsoft Windows systems, for example, they are usually displayed in the bottom right-hand corner of the screen, directly above the system clock. These so-called push notifications are based on an Internet standard designed for similar work in different operating systems and web browsers.
But many users may not fully understand what to accept when they approve the notification, or how to distinguish a message from a website that looks like a warning from an operating system or other program already installed on the device.
This is evidenced by the obvious size of the infrastructure of a relatively new company in Montenegro called PushWelcome, which enhances the ability of website owners to monetize the traffic of their visitors. Alexa.com is currently one of the top 2000 websites in terms of worldwide internet traffic.
The editors of the website that subscribes to PushWelcome are encouraged to include a small script on their site that invites visitors to approve notifications. In many cases, requests for approval of the report itself are misleading – disguised as OK to watch the video, or as CAPTCHA requests to distinguish automated robot traffic from real visitors.
A PushWelcome ad that informs you about the money that websites can earn by integrating their questionable push notification scripts.
Approval of reports from a website using PushWelcome enables each advertising partner to display the message of his or her choice at any time and in real time. And almost always these messages contain misleading references to the security risks of the user’s system, references to the installation of other software, advertisements for dating sites, erectile dysfunction and questionable investment opportunities.
This corresponds to an in-depth analysis of the PushWelcome network by Indelible LLC, a cybersecurity company based in Portland, Oregon. Frank Angiolelli, vice president of security at Indelible, said fraudulent reports can be used to phish accounts and protect users from malware and other unwanted applications.
This method is currently used to disseminate something similar to adware or click fraud, said Angiolelli. Attention is drawn to this aspect, which is so insensitive to the termination of security programmes that there is a real risk that this activity will be used for much more harmful purposes.
Sites associated with PushWelcome often use misleading messages to encourage people to approve reports.
Mr Angiolelli states that external Internet addresses, agents of browser users and other telemetry connected to persons who have accepted notifications are known to PushWelcome, enabling them to address organisations and individual users with any number of false system alerts.
It is also unknown that browser changes in PushWelcome are poorly detected by antivirus and security products, although it has been noted that malicious bytes are reliably detected as dangerous publisher websites in connection with notifications.
In fact, Pieter Arntz warned against malicious push notifications from a malicious browser in his January 2019 message. This message contains detailed instructions on how to report sites for which you have given permission to send notifications and how to delete them.
KrebsOnSecurity installed the PushWelcome notifications on the brand new Windows test computer and discovered that it received notifications of malicious threats that were supposedly detected on the system shortly afterwards. One was an ad for Norton’s antivirus program, the other for McAfee. A click on one of these sites eventually led to the purchase of sites that are now either on Norton.com or McAfee.com.
By clicking on the PushWelcome notification at the bottom right of the screen, I have opened the website and claimed that my new test system is infected with 5 viruses.
It seems that PushWelcome and/or some of its advertisers are trying to earn commissions to entice customers to buy antivirus products from these companies. McAfee has not yet responded to requests for comments. Norton makes the following statement:
We don’t believe this player is a partner of NortonLifeLock. We’re continuing our investigation into this case. NortonLifeLock takes partner fraud and abuse seriously and ensures that it is always respected. If a partner abuses its responsibility and violates our agreements, we will take the necessary steps to remove these partners from the program and terminate our relationship immediately. In addition, any commissions earned through abuse are not paid out. In addition, NortonLifeLock sends reports of partner abuse to all of our partner networks to ensure that a partner is not eligible to participate in future NortonLifeLock programs.
Requests for comments sent to PushWelcome by e-mail have been returned as undeliverable. Requests submitted via the contact form on the company’s website were also not sent.
While fraudulent reporting may not be the most urgent threat to Internet users today, most people probably don’t know how this type of communication can be abused.
Moreover, dubious alert networks can be used for less visible and less treacherous purposes, such as spreading false messages and disguising malicious software as notifications of updates to the user’s operating system. I hope it is clear that regardless of the browser, device, or operating system you are using, it makes sense to pay attention to the websites on which you allow notifications.
*** It’s the Krebs on Security network of union bloggers, written by BrianKrebs. The original message can be found at the following address: https://krebsonsecurity.com/2020/11/be-very-sparing-in-allowing-site-notifications/.
Related Tags:
veritas acquired by carlyle,veritas technologies revenue 2019,veritas technologies linkedin,carlyle group crunchbase,globanet,veritas stock price,endpoint security,sophos